2.1 Parameters
2.1.1 Summary
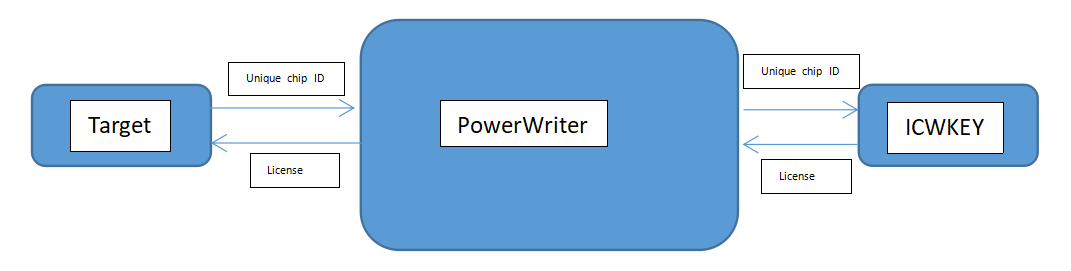
ICWorkshop is committed to empowering the traditional IC industry with Internet+ technology to provide a safer and more efficient production management model for the traditional IC production process! In order to meet the needs of users for safe chip programming, authorization control and customized production, ICWorkshop has launched the "Security Authorization Shield (ICWKEY)", hereinafter referred to as ICWKEY, which is an auxiliary tool for the offline authorization of ICWorkshop programmer, PowerWriter®, to control the number of authorizations and generate authorization keys, which ensures that the target chip + PowerWriter® + authorization key will be generated at the time of production. ICWKEY is an auxiliary tool to control the number of ICWorkshop and generate authorization keys, which can ensure the security of the entire link layer data of target chip + PowerWriter® + ICWKEY during production, ensure that the user's firmware is not illegally accessed, and ensure that the user retains the unique authorization control privileges in his hand, to prevent the possibility of unauthorized copies, ICWKEY is completely in the hands of the user, which is safe and reliable, and the following figure shows the workflow diagram:
ICWKEY provides two UID (Unique Chip ID) authorization algorithms, Vector Matrix Encryption (Matrix) and ECDSA Digital Signature, as well as an SDK for users to develop their own custom authorization algorithms to meet different needs. It provides sample programs on how to use UID authorization algorithms on target chips, and also provides ICWKEY.exe, the Windows software of ICWKEY, which allows users to import the randomly generated authorization algorithm source code of ICWKEY.exe into their own programs.
MCU General Purpose Advanced Software Protection Library can provide a higher level of protection, integrated ICWKEY signature, firmware encapsulation, firmware compression, function-level code encryption, firmware validation, object monitoring, unauthorized access detection, debugger detection, privilege separation and control, and other rich security features, to further enhance the security of the software, for more information, please email to cs@icworkshop.com get more detailed information (not currently publicly available to prevent abuse).
When using ICWKEY,suggesting to refer 《ICWKEY User Manual》.
During the project configuration, please save both the PowerWriter® project and the ICWKEY project, and remember the project password to prevent loss of configuration information, which may result in being unable to connect to the ICWKEY device.
The ICWKEY is set to allow a maximum of 65,535 uses by default. If one-time use is required, please configure the usage count to "1". Please exercise caution when setting it to one-time use in other scenarios.
:::
2.1.2 Product Parameters
- Size:57mm x 22.5mm x 10.6mm (≈)
- Operating voltage:5V (USB Type-C)
- Product Power Consumption:60mA~ 90mA
The parameters of the products are theoretical data, because of the batch, working environment, product improvement and other reasons, there may be differences in the actual, for reference only, subject to change without notice!
2.1.3 Interface

①:PowerWriter® Type-C Host Port (connected to PowerWriter®)。
②:ICWKEY OLED monitor
- Project name: Displayed in the format: SafeLic_xxxxxxxx,xxxxxxxx hash for random item names。
- Remaining/total : such as 998/1000, the number of available signatures is 998, and the total number of signatures is 1000.
③:Type-C slave port (on a computer) :ICWKEY Powered communication (connected to PC).
2.1.4 Characteristics
- Unique ID signature range can be restricted
- Number of signatures can be controlled
- Configurable number of times (reuse control)
- Authorization log query
- Signature test
- Localizations
- Signature support
- Matrix sign
- ECDSA sign
2.1.5 Safety Features
- ICWKEY Developed with a secure chip and integrated with advanced software protection libraries to protect firmware security.
- ICWKEY and PC / ICWKEY and PowerWriter® communication encryption, built-in anti-brute force breaking mechanism, can not be cracked by exhaustive password cracking.
- Data dual zone, encrypted design, power down emergency storage.
- Extra long life design.